Sanyo Tool Reset Bq8030 Datasheetarchive
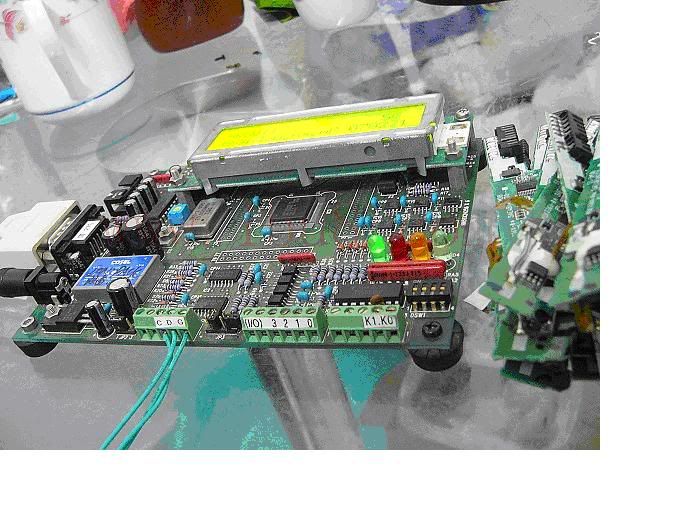
I started out by measuring voltages on all the pins. Just going by logic I was expecting some sort of differentiation on the various sides of the chip.
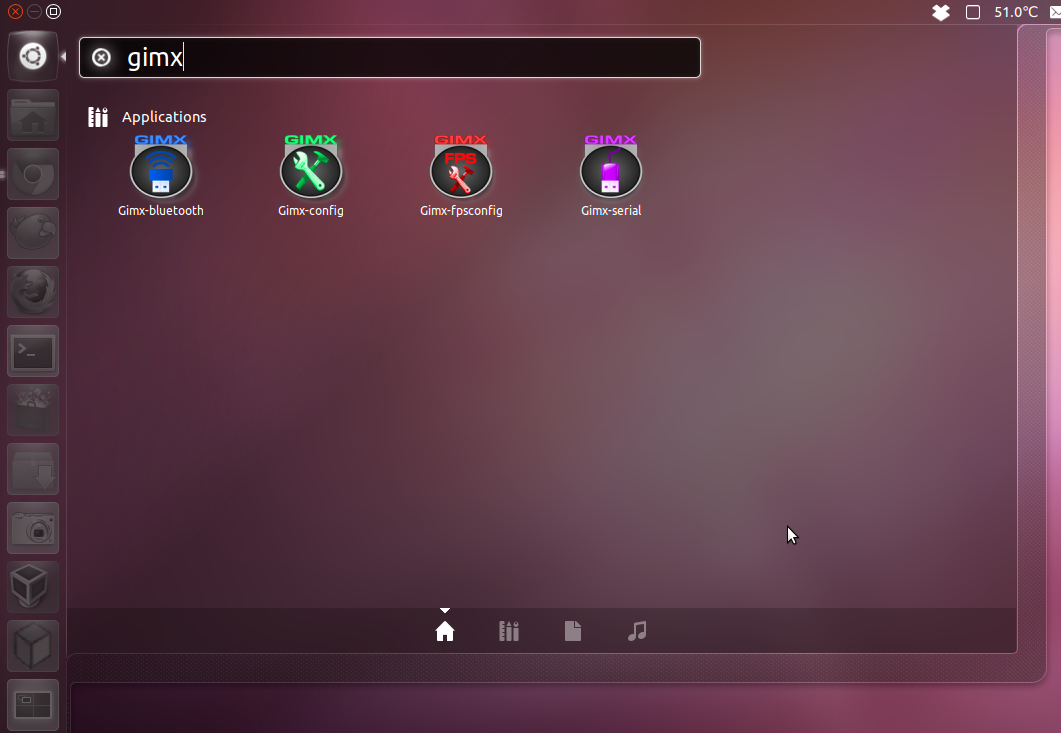
Hacking the bq8030 with SANYO firmware. As mentioned in the previous article the bq8030 is the blank version of the bq20z90. If you bought some from Aliexpress they'd come up with the TI Boot ROM and you could use the flashing tool included in SMBusb to upload firmware and eeprom (data flash) to it.
To summarize my findings after the first pass: • 1-12 is the 'main microcontroller side' has the SMBus pins, VCC (and probably RESET and others) • 25-36 is connected to current sensing and exposes various built-in voltage regulators • 37-48 appears to be mainly unused with a couple of pins at 3.3v, GPIO side? • 13-24 has many pins connected directly to 'high voltage' from the cells. I took a 1k resistor connected to ground and started poking the pins with it to find reset. It should be possible to pull reset low through 1k resistor but unlikely on VCC and it shouldn't lead to a complete reset on an unrelated pin. It's also possible to rule out most pins through visual inspection and measurement.
So long story short: Pin #12 is Reset. Next I wanted to see if there's something like a Boot pin that's going to get me a different mode when pulled either low or high during reset so I started up a continuous command scan and started poking at the pins again. Pulling Pin #4 (also connected to Test Point 1 on the other side of the PCB) low during reset gave me this. $ smbusb_scan -w 0x16 ------------------------------------ smbusb_scan ------------------------------------ SMBusb Firmware Version: 1.0.1 Scanning for command writability.
Scan range: 00 - ff Skipping: None ------------------------------------ *snip* [f0] ACK, Byte writable [f1] ACK [f2] ACK [f3] ACK [f4] ACK [f5] ACK [f6] ACK [f7] ACK [f8] ACK [f9] ACK [fa] ACK, Byte writable, Word writable, Block writable [fb] ACK, Byte writable, Word writable, Block writable [fc] ACK, Byte writable, Word writable, Block writable, >Block writable [fd] ACK, Byte writable, Word writable, Block writable, >Block writable [fe] ACK [ff] ACK The chip was ACKing on every command. A deliberate attempt at confusing any would-be attacker perhaps? The write scan however reveals that the chip is actually exposing some real functionality on some of the commands and that a couple of them violate SMBus protocol. Pin #4 appears to be BOOT (active-low). Mapping Mapping out the protocol took a while especially because it doesn't correspond to standard SMBus protocol but I was eventually able to figure out how to read and write to RAM and erase blocks of memory-mapped flash. Just writing to the appropriate address in ram (after the flash blocks have been erased) writes the flash memory which is convenient. There are several partitions of flash mapped into RAM and I'm sure I haven't found all of them.
The ones I did are included as address&length presets in the flasher tool. $ smbusb_r2j240flasher -d eep2.bin -p df2 ------------------------------------ smbusb_r2j240flasher ------------------------------------ SMBusb Firmware Version: 1.0.1 ------------------------------------ Dumping memory 0x3400-0x37ff. $ xxd eep2.bin 0000000: 0000 0000 0000 0000 0000 ffff ffff ffff. 0000010: 4c4e 562d 3432 5434 3739 3700 0000 0000 LNV-42T4797. *snip* $ smbusb_r2j240flasher -d eep3.bin -p df3 ------------------------------------ smbusb_r2j240flasher ------------------------------------ SMBusb Firmware Version: 1.0.1 ------------------------------------ Dumping memory 0xc000-0xdfff.
This Pin was discovered by simpconpedo. Discover (and save) your own Pins on Pinterest. Kazahskij drajver dlya windows 7.
$ xxd eep3.bin 0000000: 0100 0700 b801 b801 1100 0203 0201 01e3. 0000010: e6fe e3ae 7000 e0e4 0cc8 0038 3150 14f0.p.81P. 0000020: 1530 2a4c 4743 0031 3100 0000 0000 0000.0*LGC.11.